Back in 2015, I have published a blog post titled "Pwning a thin client in less two minutes" which attracted a lot of curiosity from the Internet and which was also featured in the HACKADAY blog.
Today, together with Vincent Hutsebaut (@vhutsebaut), we are releasing a further technique to pwn the same thin client and get a root shell without authentication, in less than one minute!
The attack detailed below is a typical kiosk attack which consists in a local privilege escalation which affects different versions of HP Thin Pro OS (HP ThinPro 4.4, HP ThinPro 5.0, HP ThinPro 5.1, HP ThinPro 5.2, HP ThinPro 5.2.1, HP ThinPro 6.0, HP ThinPro 6.1).
The vulnerability (CVE-2016-2246) has been patched by HP and a technical bulletin has been published. HP stated that they have fixed the issue before our report was sent to them and were on the way to publish a security bulletin when we contacted them.
Since the patch is out, let's dive into the vulnerability, which is detailed step by step below.
For those of you in rush, feel free to skip to the bottom of this post and watch the video.
As usual, if you enjoy it, the authors would love to see this article shared and retweeted ;-)
Description
In HP Thin Pro OS, the sudo configuration allows an unauthenticated user to abuse the keyboard layout tool to perform a privilege escalation attack and gain unauthorised root access on the machine.
The keyboard layout (located in "/usr/bin/hptc-keyboard-layout") runs as a privileged process and it is directly available to an unauthenticated user from the UI (user interface) of the HP Thin Pro Kiosk.
By abusing the available UI controls, an unauthenticated user can navigate on the file system and restore the original /etc/shadow file on the system, which will then allow to set a new admin password on the system.
Conditions
The following conditions are required:
- HP Thin OS Pro set in Kiosk mode;
- HP Thin OS Pro administrator password has already been set by an administrator;
- A malicious user has physical access to the Kiosk but does not have a user account and does not know the admin password.
Steps to reproduce (as a malicious user)
1) Click on the left side, "Control Panel" icon and then clicking the "Keyboard Layout" icon; ** note that the button and UI might be different from the OS version, but the keyboard layout tool is available to an unauthenticated user in Kiosk mode
Step 1 – Figure 1
2) Click on print icon, a "Print File" dialog prompt is provided to the user
Step 2 – Figure 1
3) Print File dialog allows to set an "output file" - by clicking on the "..." button to choose the folder
Step 3 – Figure 1
Step 3 – Figure 2
4) Navigate to /etc/ folder
Step 4 – Figure 1
5) Rename /etc/shadow into /etc/shadow-last-modified-by-admin
Step 5 – Figure 1
Step 5 – Figure 2
6) Rename /etc/shadow- into /etc/shadow
Step 6 – Figure 1
7) Click on the "Administrator/User Mode Switch"
Step 7 – Figure 1
8) Malicious user can set a new admin password and access the administrator mode of the kiosk
Step 8 – Figure 1
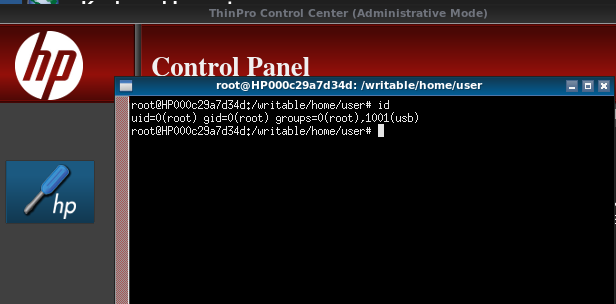
9) Launch an xterminal with root access
Step 9 – Figure 1
Step 9 – Figure 2
Further observations
The /etc/shadow- file remains as the original one even after that the admin password has been changed multiple times. In this example, passwd has already been set twice but the shadow- remains the one set originally in the OS (back in 2013), making the attack described possible.
In the sudoer configuration, it is possible to see the NOPASSWD tag set for the Keyboard Layout tool (usr/bin/hptc-keyboard-layout):
Below, a video showing the entire sequence:
If you like kiosks and more in particular you like to break them, then you absolutely need to try: http://ikat.ha.cked.net/ . Greetz to Paul Craig, the "self-proclaimed" king of kiosks! ;-)













Very nice !!!
ReplyDeleteWell done !!
Very fricking nice - I had never thought of something like this!
ReplyDeleteThank god they patched it!